Why Being Smart About Cybersecurity Is Key To Protecting Your Personal Data
Cybersecurity has been a major concern in recent days, after a cyberattack on SingHealth led to the personal data of 1.5 million Singaporeans being stolen.
And more recently, some local Apple customers complained of mysterious iTunes purchases that amounted to thousands of dollars.
So what’s happening to our nation’s cyber security, which the United Nations ranked top in the world last year?
As the Government investigates the culprits of the cyberattacks, we think Singaporeans should take it upon themselves to safeguard their data online.
So here are 12 things you can do right away to beef up your cyber security:
Browsing Habits
1) Use secure alphanumeric passwords
Pet names, birthdays and names of loved ones: these are often the inspiration for our passwords.
But they also happen to be some of the worst passwords around, as anyone who knows anything about you can guess them quite easily.
Instead, why not come up with an alphanumeric password to provide actual security for your devices?
Play around with punctuation marks and capitalised letters. So instead of chocolate, try something like Ch0c0l@t3.
2) Set up PINs & 2FAs
PINs and 2-Factor Authentication (2FA) serve as an extra layer of security for your devices.
PINs on phones and tablets are akin to passwords for computers, preventing unauthorised access.
On the other hand, 2FA is useful when performing sensitive transactions. It requires users to key in extra information, which may come through an SMS to a linked phone number or information on a physical token.
2FA is usually instituted by organisations like the Government and banks, but you can also use it for your emails and social media accounts.
Having this extra layer of security prevents fraudulent transactions.
3) Don’t store passwords on devices
At least 1 in 3 store passwords on computers, according to a 2017 Cyber Security Agency of Singapore (CSA) survey.
And if that’s anything to go by, there must be a significant number who store passwords on their phones and tablets as well.
It’s not just physically writing down your passwords on your devices that’s dangerous.
Having web browsers and password managers “remember” passwords is also risky, since a hacker with access to your device can easily access all these accounts.
Similarly, when a device is lost, anyone who finds it and manages to break into it will also have access to all the accounts stored in it.
4) Clear browser cookies and cache regularly
Even though some may do it for other reasons, clearing your browsing history and cookies periodically can help safeguard your data.
Cookies, along with browsing history, help accelerate a user’s browsing experience by tracking what they do online.
This includes everything from their login credentials to their purchases.
Enabling cookies for a long time means that all this personal data is held on third-party websites, which are just as vulnerable to data hacks as you are.
Avoid Scams
5) Use public Wi-Fi cautiously
More than 3 in 5 of respondents to another CSA survey admitted to connecting to unsecured WiFi networks that were not password protected, despite not being familiar with the network.
While this is a great data-saving hack, it’s a foolish thing to do from a cybersecurity angle.
That’s because these networks may have been intentionally set up by hackers to access personal information like their bank details.
6) Never leave devices unattended
Your device may not be physically stolen but leaving it unattended can result in the theft of personal information.
You may think that it won’t be a problem since you’re just leaving it for a couple of minutes.
But a lot can happen in that period. A few minutes with an unattended laptop is all hackers need to install a virus capable of accessing your personal information.
7) Only disclose sensitive information to verified sources
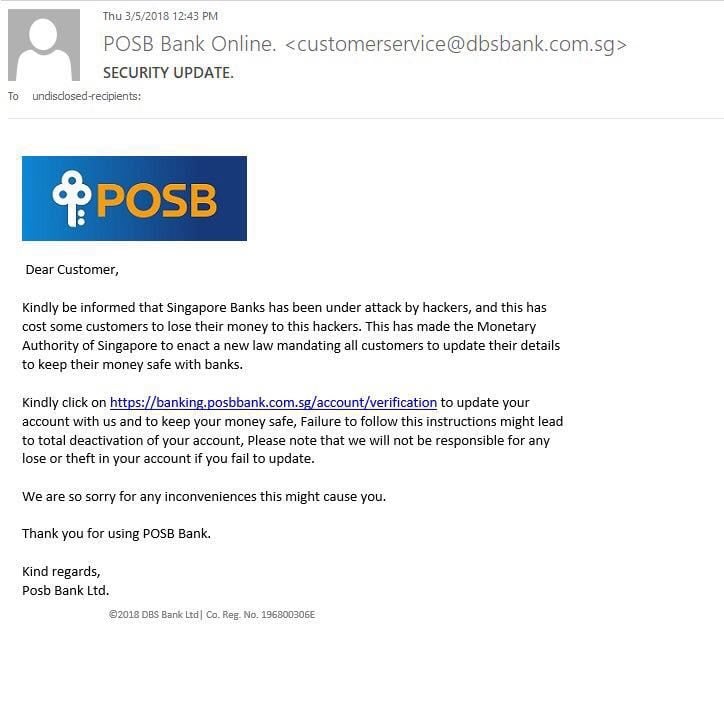
Hackers may disguise themselves as established companies in order to get sensitive information from users — also known as phishing.
The concept of phishing is largely similar to the recreational activity that it shares the same pronunciation with — fishing.
Instead of fishing bait, users are ‘baited’ into disclosing their personal information and password by clicking on a link that brings them to a separate page resembling a reputable company.
Except it’s not the real deal.
These phishing attempts may come in the form of emails or text messages.
Established companies such as Apple have put in place guidelines to help users avoid falling victim to phishing scams. So do check with the company in question should you come across a suspicious email.
8) Be wary when granting app permissions
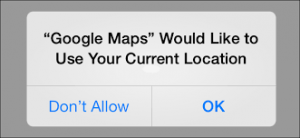
After installing an app, a window often pops up on the phone prompting the user to grant certain permissions for the app to work properly.
While it might be tempting to click ‘allow’ for these permissions, we need to keep in mind which permissions these apps actually need to function.
Flash Keyboard, a popular app on Android devices, requested users to provide access to their camera, location and even their lock screen displays — more permissions than it actually needed to operate.
The app was caught tracking its users, showing them malicious ads and transferring data harvested to China.
Back up & install anti-virus software (and keep them updated)
9) Back up data regularly
It is extremely important for users to back up their devices from time to time, eventhough it takes up a significant of disk space and time. You never know when it’s gonna pay off.
Ransomware, a kind of malware, restricts a user’s access to his/her device unless a ransom is paid.
Permanent loss of information may occur, unless there is a backup version of the device before the attack.
10) Install anti-virus protection
Anti-virus software help to deter, detect and remove software viruses from our devices. As such, having an anti-virus software is almost vital to maintaining a virus-free device.
While most people know that anti-virus software exist for our computers, some do not know that they exist for our handphones as well.
Our handphones contain a lot of our personal information, ranging from card details to location information to even our personal photos and videos.
So it’s only wise that we give our phones the same level of protection as our computers.
11) Keep your software up-to-date
We often see updates as an inconvenience because of the massive file installation and lengthy process involved. But updates are necessary to close loopholes that hackers can exploit.
So even though it might take a few minutes of your time, it is in your interest to update your apps to the latest available versions.
12) Turn off your computer. Don’t put it to sleep.
Many of us are guilty of this — not turning our computers off but putting them to sleep instead.
After all, it’s the fastest and most convenient way to put our computers to ‘rest’.
While it’s acceptable to put a computer to sleep for a short period of time, putting it to sleep for long periods may potentially put our computers – and data – at risk.
A computer on sleep mode can still be accessible by a hacker, even though it is not being used.
On the other hand, turning the computer off will eliminate any possibility of a hacker getting access to it.
Take cybersecurity seriously
We think it goes without saying that more should be done to improve our cybersecurity, since we live in a time when most of our personal information is stored electronically.
Yet on a personal level, we think more of us can do more to safeguard our personal information.
So what’s stopping you from taking the first steps to doing it?
Featured image from SecurityIntelligence.